Who Is Calling Me – Identify and Block Unknown Callers
Unknown numbers disrupt daily routines and raise privacy concerns for millions of mobile users. Whether the caller ID displays “Unknown Caller,” a private number, or an unrecognized area code, identifying the source requires understanding available identification methods and potential risks.
Modern smartphones offer built-in screening features, while third-party applications access extensive databases to match numbers with identities. Regulatory frameworks from agencies like the Federal Trade Commission provide additional consumer protections against unwanted solicitations.
This guide examines practical approaches to reveal caller identities, evaluates identification technologies, and outlines legal rights regarding unsolicited communications.
How Do I Find Out Who Is Calling Me?
Identifying an unknown caller involves combining built-in phone features, online services, and pattern recognition. The method effectiveness varies based on whether the number appears as “Unknown,” “Private,” or shows a visible string of digits.
Quick Lookup Tools
Reverse phone lookup websites compare entered digits against public directories and user-reported databases.
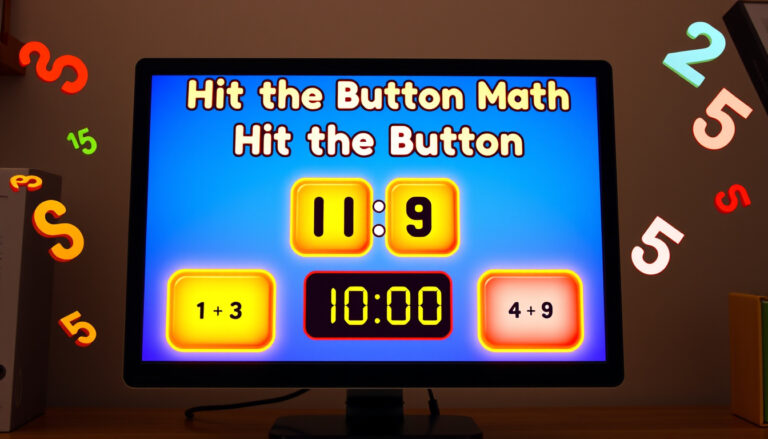
Top Free Apps
Applications like Truecaller and community platforms such as WhoCallsMe crowdsource identification data.
Spam Indicators
Unexpected international prefixes, automated messages, or robotic voice patterns often signal unsolicited commercial calls.
Block Methods
Both iOS and Android systems provide native blocking features accessible through recent call logs or security settings.
Key Identification Insights
- Reverse lookups work best with full 10-digit numbers rather than “Private” or “Unknown” displays
- Community-driven platforms rely on user submissions, creating varying accuracy levels
- Carrier-grade authentication services help verify legitimate business calls
- Free lookup tools typically provide basic location data while charging for detailed owner information
- International numbers often bypass domestic do-not-call registries
- SIM-based caller ID features function without internet connectivity
- Law enforcement tracing requires legal documentation and carrier cooperation
Essential Facts About Unknown Calls
| Aspect | Details | Implication |
|---|---|---|
| Number Display Types | Visible digits, Private, Unknown, or Blocked | Determines available identification methods |
| Lookup Accuracy | Varies by database freshness and user participation | Results may show previous owners or incorrect data |
| Legal Protections | FCC regulations mandate consent for marketing calls | Consumers may report violations to authorities |
| App Permissions | Caller ID apps require phone and contact access | Privacy trade-offs exist for identification services |
| Carrier Tools | Major providers offer free spam filtering | Network-level blocking reduces device storage needs |
| International Calls | Often originate from VoIP services masking true locations | Tracking and legal recourse become complicated |
| Reporting Mechanisms | FTC complaint portals document illegal activity | Aggregated data drives enforcement actions |
| Verification Standards | STIR/SHAKEN protocols authenticate caller IDs | Legitimate calls display “Verified” labels on compatible devices |
What Are the Best Apps to Identify Unknown Callers?
Selecting an identification service requires evaluating database size, privacy policies, and platform compatibility. Nomorobo specializes in landline and VoIP blocking, while database services like Whitepages offer detailed owner histories for listed numbers.
Community-Based Solutions
Platforms relying on user-generated content, such as WhoCallsMe, allow individuals to report nuisance numbers and share experiences. These services excel at identifying emerging spam campaigns but may lack verification for newer legitimate business lines.
Integrated System Features
Modern operating systems incorporate screening technologies that transcribe voicemails in real-time or silence unknown callers automatically. These native tools require no additional downloads and function offline using locally stored pattern recognition.
Many free caller ID applications monetize through data collection, uploading user contact lists to improve their databases. Reviewing permissions before installation helps maintain contact confidentiality.
Is the Unknown Number Calling Me a Scam?
Determining malicious intent involves analyzing call patterns, content, and urgency tactics. Consumer protection resources indicate that legitimate organizations rarely demand immediate payment or sensitive personal information via unsolicited calls.
Common Fraud Indicators
Pressure to act immediately, threats of legal action, or requests for payment via gift cards or cryptocurrency represent standard scam methodologies. Callers claiming affiliation with government agencies while requesting financial information warrant particular scrutiny.
Verification Techniques
Ending suspicious calls and independently contacting the purported organization through official channels confirms legitimacy. Searching number databases alongside keywords like “scam” or “complaint” often reveals other recipients’ experiences.
How to Block Spam Calls and Unknown Numbers?
Prevention strategies range from device-specific settings to network-level filters provided by telecommunications carriers. Federal guidelines require phone companies to offer robocall blocking tools without additional charges.
Native Device Controls
Both major mobile operating systems allow users to silence all unknown callers, sending them directly to voicemail. This setting distinguishes between numbers saved in contacts and all other incoming attempts.
Carrier-Level Protection
Major wireless providers deploy analytics engines that identify likely spam before phones ring. These services often categorize risks as “High,” “Medium,” or “Low” based on calling patterns and user reports.
When private numbers call repeatedly despite blocking attempts, documenting call times and content supports potential legal action. Resources like Martin Lewis Phone Security Code provide additional consumer protection guidance.
The Telephone Consumer Protection Act restricts automated calls to mobile devices without prior consent. Violations may result in statutory damages, with complaints filed through the FTC’s Do Not Call Registry.
Common Spam Call Trends Timeline
Unwanted calling patterns have evolved significantly over recent years, with scammers adapting to technological defenses and regulatory changes.
- : Surge in COVID-19 related contact tracing impersonations and stimulus check scams, as documented by FTC consumer alerts.
- : Widespread implementation of STIR/SHAKEN caller ID authentication protocols by major carriers to combat spoofing.
- : Increase in “neighbor spoofing” using local area codes to increase answer rates, prompting enhanced filtering algorithms.
- : Financial institution impersonation schemes targeting mobile banking users through voice phishing combined with SMS follow-ups.
- : AI-generated voice cloning technology enabling more convincing family emergency scams and extortion attempts.
- : Integration of advanced call screening with smart home ecosystems and vehicle interfaces to minimize driving distractions.
Known vs Unknown About Callers
| Established Information | Uncertain or Context-Dependent Factors |
|---|---|
| Caller ID spoofing technology allows display of false numbers | Whether a specific unknown call originates domestically or internationally |
| Do Not Call Registry enrollment expires after ten years | Whether repeated calls represent coordinated harassment or independent autodialers |
| Legitimate businesses honor opt-out requests | The exact identity behind “Private” or “Unknown” displays without carrier intervention |
| Free lookup services provide limited data compared to paid alternatives | Whether voice patterns indicate live callers or advanced AI simulations |
| Regulatory agencies maintain complaint databases | The likelihood of recovering funds lost to successful phone scams |
Why Unknown Calls Happen & What They Mean
Unknown calls originate from diverse sources including legitimate businesses using autodialers, market research firms, political campaigns, and fraudulent operations. The prevalence of Voice over Internet Protocol (VoIP) technology reduces calling costs to near zero, enabling high-volume campaigns that blanket entire area codes sequentially.
Telemarketing operations often purchase lead lists containing consumer contact information gathered from online forms, warranty registrations, or data brokers. Meanwhile, scam networks operate across international borders, exploiting jurisdictional complexities that complicate law enforcement coordination. Understanding these mechanisms helps distinguish between nuisance marketing and criminal intent.
Drivers receiving unexpected calls face additional safety considerations. Distraction from unknown numbers contributes to roadway incidents, making identification and blocking tools essential before operating vehicles. Resources covering Car Dashboard Symbols and Meanings emphasize managing in-cabin technologies safely to maintain focus on traffic conditions.
Expert Sources & Data
Regulatory bodies provide authoritative guidance on consumer rights and industry standards. The Federal Trade Commission maintains the national Do Not Call Registry and publishes enforcement data regarding robocall violations. The Federal Communications Commission mandates technical standards including caller ID authentication to restore consumer trust in displayed numbers.
Consumer education resources from consumer.ftc.gov detail recognition patterns for fraudulent communications. Independent analysis from How-To Geek offers technical explanations of blocking mechanisms and database limitations.
Next Steps to Protect Yourself
Begin by registering your number with the FTC Do Not Call Registry, then activate native spam filtering features on your device. Evaluate third-party identification applications based on privacy policies that align with your data-sharing comfort level, and report persistent violations to regulatory authorities to support broader enforcement efforts.
Additional Questions About Unknown Callers
Why is a private number calling me?
Private numbers indicate the caller deliberately blocked their identity using *67 or organizational privacy settings. Medical facilities, law offices, and confidential support lines frequently use this feature legitimately, though scammers exploit it to avoid detection.
Can I trace calls without apps?
Basic tracing requires noting exact times and dates, then contacting your carrier for call detail records. Law enforcement can subpoena origin data for serious harassment cases, though this process requires documentation of multiple incidents.
Are free reverse lookups reliable?
Free services typically identify only publicly listed landlines or businesses. Mobile numbers and unlisted lines often return no results or outdated information previously associated with the number.
Will blocking stop all spam?
Blocking reduces but cannot eliminate all unwanted calls, as spoofers constantly rotate through new number combinations. Layered defense combining carrier tools, device settings, and cautious answering habits provides optimal protection.
How do I report international scam calls?
Document the number and any recorded messages, then file complaints with both the FTC and your carrier. International law enforcement coordination handles severe fraud networks, though individual recovery remains challenging.